Overview
Cyber Awareness Risk Management (CARM) a low-cost Human Risk Management service that is quick to launch, non-disruptive and covers all of the key elements for driving secure user behaviour, including:
- Engaging and bite-sized security awareness training programs
- Regular simulated phishing assessments
- Continuous dark web monitoring
- Essential policy implementation with trackable staff signatures
- Ongoing human risk scoring and regular summary reports
- Readily-made courses, phishing templates and policy documents
How will CARM training work?
Gap Analysis
Once onboarded, users will be emailed a short Gap Analysis Questionnaire to complete. The questionnaire will measure your current security knowledge and help identify areas that need improvement.
This only takes between 5-10 minutes to complete and provides the baseline on what topics users need to be trained on first.
Security Awareness Courses
Once the Gap Analysis has been completed, users will receive an email with an invitation to access the first course. Depending on how your Gap Analysis went you will be enrolled in a course that helps you bridge the gap on the lowest area you scored in. Courses include a short video, and after the video a short test to check the knowledge is retained.
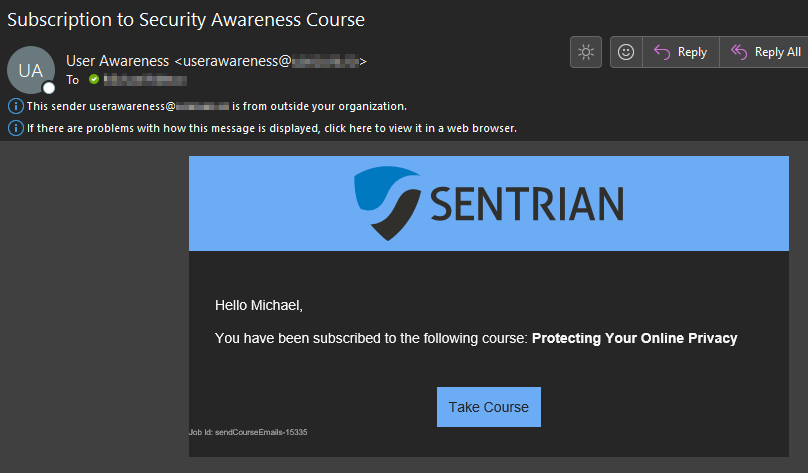
Below is an example of a course video and other topics covered:
- Phishing Awareness
- Secure Passwords & Authentication
- Security at Home
- Public Wi-Fi
- Secure Internet Use
- Protecting Your Online Privacy
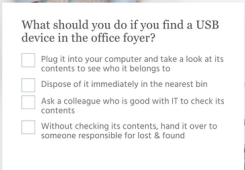
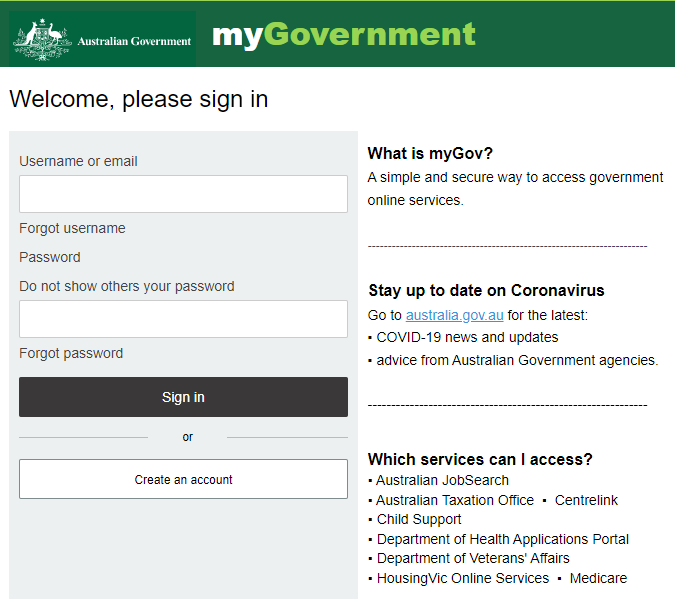
Automatic Phishing Simulation
CARM includes phishing simulation software that sends out emails that are disguised to look like legitimate emails to quickly assess user vulnerability towards real-world phishing attacks. This helps identify which users are susceptible to both common forms of phishing and targeted forms of ‘spear phishing’.
Key features:
- Accurately determine user vulnerability towards phishing
- Identify users that need urgent phishing awareness training
- Reduce the likelihood of users falling victim to future phishing attacks
- Develop a security-minded culture in your organisation
- Regular phishing simulations – allowing you to assess user performance over time.
- Access a library of phishing emails and landing pages impersonating trusted organisations, banks, government departments, and more.
Example Phishing email sent to users:
Policy Management
Policy management will help audit which users have or have not acknowledged approved business policies and procedures. Additionally, this helps:
- Centralising your policies
- Create, add and amend with ease
- Keep things organised with version control
- Newly onboard users automatically have the business polices sent to them to review and approve
Dark Web Monitoring
All users who are signed up automatically have the dark web monitored for their work email address. This will monitor for what breach they were part of, when they were breached, when they were added online, and also what category of information was breached.
